Press release
Vulnerability Management Market Size will Escalate Rapidly in the 2018
Vulnerability is defined as the weaknesses in the software program that allows an unauthorized user to access the sensitive data or gain control over the data of authorized users. Vulnerability management is the practice of securing the confidential data by removing the weaknesses from the computerized digital technology.A sample of this report is available upon request @ https://www.transparencymarketresearch.com/sample/sample.php?flag=B&rep_id=566
The global market for vulnerability management is expected to reach USD 1,322.6 million by 2014, growing at a CAGR of 14.2%, driven by growing number of cyber threats and emergence of new form of threats. Vulnerability management is also witnessing incorporation of IPs and network firewalls with vulnerability assessment scanning for proactive defense. However, the major challenge to the growth of this industry is integration issues with previously installed systems.
Worldwide, organizations are looking for advanced ways to secure their data and manage complex data center infrastructures. Need for faster employment of data-centers is currently driving the vulnerability management market. The ability of containerized data centers to offer flexible solutions is the major driver for the vulnerability management market. Reduction in cost of vulnerability management services and growing availability of service providers is expected to drive the market in the future.
Vulnerability management plays a key role in the telecom industry. The vulnerability management market for telecom service providers is expected to reach USD 183.2 million by 2014 due to the emergence of network specific attacks. Vulnerability management in the telecom service providers market is also helping in adoption of level scanning technique that helps to scan particular application and provide better solutions.
Some of the major players dominating the vulnerability management market include Hewlett-Packard, McAfee, IBM Corp., Symantec, Qualys Inc., GFI Software, and others.
To view TOC of this report is available upon request @ https://www.transparencymarketresearch.com/sample/sample.php?flag=T&rep_id=566
As hackers are shifting their focus from server-side vulnerabilities to client-side vulnerabilities, vendors are also expanding their product capabilities for applications such as databases, web applications, configurations among others. Novel technologies like cloud computing, bring-your-own-device (BYOD), and virtualization are helping in managing the sensitive data; however, it is also opening the door for new data security threats.
About US
Transparency Market Research (TMR) is a next-generation provider of syndicated research, customized research, and consulting services. TMR’s global and regional market intelligence coverage includes industries such as pharmaceutical, chemicals and materials, technology and media, food and beverages, and consumer goods, among others. Each TMR research report provides clients with a 360-degree view of the market with statistical forecasts, competitive landscape, detailed segmentation, key trends, and strategic recommendations.
Contact Us-
U.S. OFFICE:
State Tower,
90 State Street,
Suite 700,
Albany NY - 12207
This release was published on openPR.
Permanent link to this press release:
Copy
Please set a link in the press area of your homepage to this press release on openPR. openPR disclaims liability for any content contained in this release.
You can edit or delete your press release Vulnerability Management Market Size will Escalate Rapidly in the 2018 here
News-ID: 761583 • Views: …
More Releases from Transparency Market Research
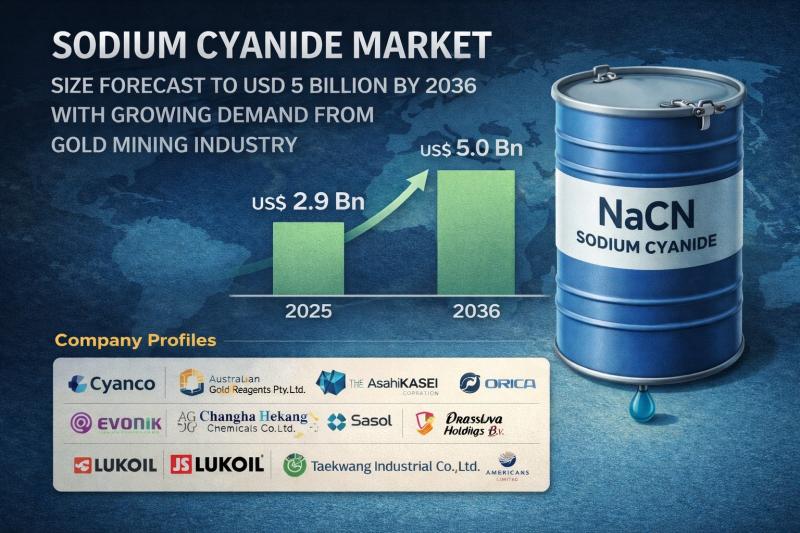
Sodium Cyanide Market Size Forecast to USD 5 Billion by 2036 with Growing Demand …
Sodium Cyanide Market Outlook 2036
The global sodium cyanide market was valued at US$ 2.9 Bn in 2025 and is projected to reach US$ 5 Bn by 2036, expanding at a CAGR of 5.2% from 2026 to 2036. Market growth is driven by increasing demand for gold extraction, rising mining activities, and technological advancements in cyanidation processes.
👉 Get your sample market research report copy today@ https://www.transparencymarketresearch.com/sample/sample.php?flag=S&rep_id=46848
Market Overview
Sodium cyanide is a highly…

Ion Implanter Market Size Forecast to USD 3.7 Billion by 2036 with Growing Semic …
Ion Implanter Market Outlook 2036
The global ion implanter market was valued at US$ 2.1 Bn in 2025 and is projected to reach US$ 3.7 Bn by 2036, expanding at a steady CAGR of 5.0% from 2026 to 2036. Market growth is driven by increasing demand for advanced semiconductor devices, expansion of consumer electronics production, and rapid developments in automotive electronics and power devices.
👉 Get your sample market research report copy…
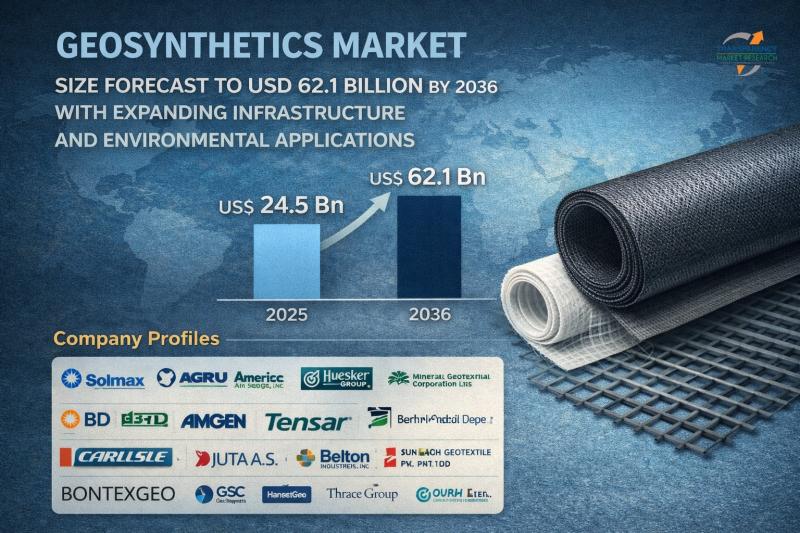
Geosynthetics Market Size Forecast to USD 62.1 Billion by 2036 with Expanding In …
Geosynthetics Market Outlook 2036
The global geosynthetics market was valued at US$ 24.5 Bn in 2025 and is projected to reach US$ 62.1 Bn by 2036, expanding at a strong CAGR of 8.8% from 2026 to 2036. Market growth is driven by increasing infrastructure development, rising demand for sustainable construction solutions, expanding waste management projects, and growing adoption in transportation and water management applications.
👉 Get your sample market research report copy…
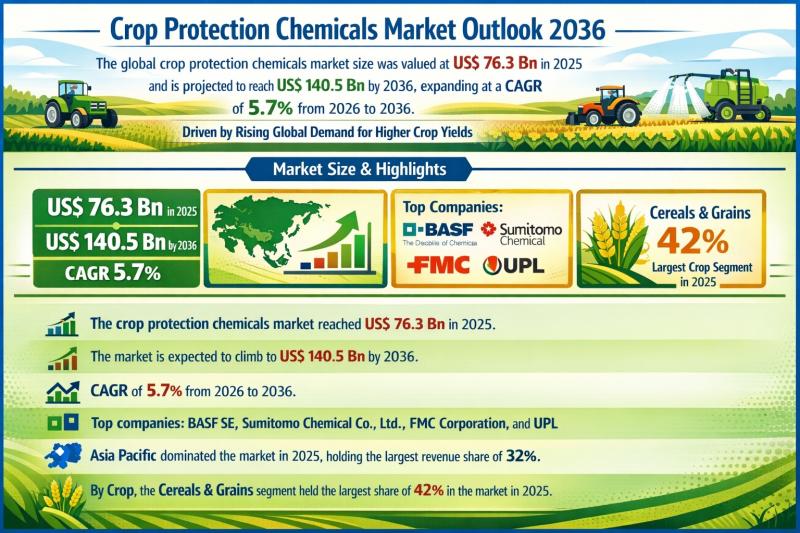
Crop Protection Chemicals Market Outlook 2036: Global Industry to Reach US$ 140. …
Crop Protection Chemicals Market Outlook 2036: Global Industry to Reach US$ 140.5 Billion at 5.7% CAGR Driven by Rising Demand for Higher Crop Yields and Food Security
The global crop protection chemicals market was valued at US$ 76.3 Bn in 2025 and is projected to reach US$ 140.5 Bn by 2036, expanding at a steady CAGR of 5.7% from 2026 to 2036. The industry's consistent growth trajectory reflects the mounting pressure…
More Releases for Vulnerability
Hazard Vulnerability Analysis for Healthcare Facilities Market Surges Amid Clima …
InsightAce Analytic Pvt. Ltd. announces the release of a market assessment report on the "Global Hazard Vulnerability Analysis For Healthcare Facilities Market- (By Type (Natural Disasters (Floods, Earthquakes, Hurricanes, Others), Technological Hazards (Chemical Spills, Power Outages, Others), and Biological Hazards (Pandemics, Epidemics, Others)), By Healthcare Facility (Hospitals, Clinics, Long-term Care Facilities, Ambulatory Surgical Centres, and Others)), Trends, Industry Competition Analysis, Revenue and Forecast To 2031."
According to the latest research by…
Vulnerability Management Tools Market
The "Vulnerability Management Tools Market" is expected to reach USD xx.x billion by 2031, indicating a compound annual growth rate (CAGR) of xx.x percent from 2024 to 2031. The market was valued at USD xx.x billion In 2023.
Growing Demand and Growth Potential in the Global Vulnerability Management Tools Market, 2024-2031
Verified Market Research's most recent report, "Vulnerability Management Tools Market: Global Industry Trends, Share, Size, Growth, Opportunity and Forecast 2023-2030," provides…
Vulnerability Management Software Market
The "Vulnerability Management Software Market" is expected to reach USD xx.x billion by 2031, indicating a compound annual growth rate (CAGR) of xx.x percent from 2024 to 2031. The market was valued at USD xx.x billion In 2023.
Growing Demand and Growth Potential in the Global Vulnerability Management Software Market, 2024-2031
Verified Market Research's most recent report, "Vulnerability Management Software Market: Global Industry Trends, Share, Size, Growth, Opportunity and Forecast 2023-2030," provides…
AI Vulnerability Scanning Market Size | Valuates Reports
AI Vulnerability Scanning Market Size
In order to maintain its leading position, the United States will increase its investment in artificial intelligence research and development in non-defense fields, from US$1.6 billion to US$1.7 billion in 2022.
View Sample Report
https://reports.valuates.com/request/sample/QYRE-Auto-12L15782/Global_AI_Vulnerability_Scanning_Market_Research_Report_2023
Report Scope
The growing use of AI technology across a range of industries, which also raises the risk of vulnerabilities and cyber attacks, is driving the market for AI vulnerability scanning. AI is being used…
Vulnerability Assessment Solutions Market 2021 | Detailed Report
Vulnerability Assessment Solutions Market Forecasts report provided to identify significant trends, drivers, influence factors in global and regions, agreements, new product launches and acquisitions, Analysis, market drivers, opportunities and challenges, risks in the market, cost and forecasts to 2027.
Get Free Sample PDF (including full TOC, Tables and Figures) of Vulnerability Assessment Solutions Market @ https://www.reportsnreports.com/contacts/requestsample.aspx?name=5016573
The report provides a comprehensive analysis of company profiles listed below:
- Tenable
- Rapid7
- Qualys
- GFI…
Compliance Combines with Vulnerability Scanning to Create Aegify
SANTA CLARA, Calif., December 11, 2012 - Two security firms, the established Rapid7 vulnerability manager and eGestalt, a cloud-based compliance management provider, have signed an OEM deal that will do something for the IT security industry that hasn't been done before: a combination security and compliance posture management offering called Aegify SPM.
The SPM stands for Security Posture Management, and eGestalt of Santa Clara defines SPM as "the art and science…
