Press release
What Should Be on Your CMMC Compliance Checklist?
In today's cybersecurity climate, compliance isn't just a best practice-it's a necessity. For contractors and subcontractors in the U.S. defense industrial base (DIB), adhering to the Cybersecurity Maturity Model Certification (CMMC) is essential for maintaining eligibility for Department of Defense (DoD) contracts. The process of achieving and maintaining certification can be complex, but a well-structured CMMC compliance checklist (https://www.lgnetworksinc.com/what-is-cmmc-compliance/) can provide clarity, structure, and momentum.Whether you're preparing for your first CMMC assessment or planning to level up to a higher maturity level, this comprehensive checklist will help ensure you're on the right track.
• What is CMMC?
The Cybersecurity Maturity Model Certification is a unified standard created by the DoD to ensure all its contractors have robust cybersecurity measures in place to protect Controlled Unclassified Information (CUI) and Federal Contract Information (FCI).
CMMC is evolving-CMMC 2.0 is the latest iteration, reducing five maturity levels to three and streamlining requirements for many organizations. But regardless of which version you're preparing for, the core principles of cybersecurity hygiene, risk management, and continuous improvement remain intact.
• Why You Need a CMMC Compliance Checklist
Given the complexity and depth of CMMC requirements, a structured compliance checklist provides multiple advantages:
Organization: Tracks progress across dozens of practices and processes.
Readiness: Prepares you for third-party assessments or self-assessments.
Risk Mitigation: Helps identify and close security gaps before they become breaches.
Contract Eligibility: Demonstrates your eligibility for DoD contracts, increasing competitiveness.
Let's break down the essential components of a robust CMMC compliance checklist.
1. Determine Your Required CMMC Level
The first step is identifying which CMMC level applies to your organization:
Level 1: Basic cyber hygiene, required for handling FCI.
Level 2: Intermediate cyber hygiene, required for handling CUI. Equivalent to NIST SP 800-171.
Level 3: Expert cybersecurity, aligned with a subset of NIST SP 800-172.
📌 Checklist Item:
☐ Review your contracts to determine whether you handle FCI, CUI, or both.
☐ Confirm which CMMC level your organization must meet.
2. Understand CMMC Domains and Practices
CMMC is built around cybersecurity domains, such as:
Access Control (AC)
Incident Response (IR)
Risk Management (RM)
System and Communications Protection (SC)
Each domain contains a series of practices (technical requirements) and processes (management maturity).
📌 Checklist Item:
☐ Download and study the latest CMMC Assessment Guide for your required level.
☐ Map each domain's practices to your current IT and security controls.
3. Perform a Gap Analysis
A gap analysis compares your current cybersecurity posture to CMMC requirements. It helps you understand what's already in place and what needs improvement.
📌 Checklist Item:
☐ Conduct a self-assessment using tools like the DoD's Project Spectrum or NIST 800-171A.
☐ Document areas of non-compliance or missing controls.
☐ Prioritize remediation efforts based on risk.
4. Develop and Update Policies and Procedures
Many CMMC practices require documented, consistently applied policies and procedures. If you don't have formal documentation-or if it's outdated-now is the time to write or revise it.
📌 Checklist Item:
☐ Create or update policies for access control, incident response, configuration management, and more.
☐ Ensure procedures are aligned with CMMC requirements and reflect actual operational practices.
☐ Implement policy training for staff.
5. Implement Technical Controls
This is where cybersecurity tools and infrastructure come into play. Many CMMC practices require organizations to deploy specific technical safeguards.
📌 Checklist Item:
☐ Enforce Multi-Factor Authentication (MFA) for all sensitive systems.
☐ Configure audit logs and ensure log monitoring is in place.
☐ Use encryption for data in transit and at rest.
☐ Harden endpoint devices and restrict access via role-based access control.
6. Establish an Incident Response Plan (IRP)
Incident response is a critical focus of CMMC. You must be prepared to detect, report, and recover from cybersecurity incidents efficiently.
📌 Checklist Item:
☐ Develop a formal IRP with defined roles, responsibilities, and escalation paths.
☐ Conduct tabletop exercises or simulations to test response capabilities.
☐ Document lessons learned and update your IRP regularly.
7. Control and Monitor Access to Systems
Access Control (AC) is one of the most heavily weighted domains in CMMC. You must limit access to authorized users and monitor user activity.
📌 Checklist Item:
☐ Review user access rights regularly and remove unnecessary privileges.
☐ Use centralized identity and access management (IAM) tools.
☐ Set up logging and alerts for anomalous behavior or unauthorized access attempts.
8. Train Your Team on Cybersecurity Awareness
Employees can be the weakest link or your first line of defense. Ongoing training is essential to meet CMMC's expectations around awareness and responsibility.
📌 Checklist Item:
☐ Conduct mandatory cybersecurity training for all staff at least annually.
☐ Include phishing awareness, password hygiene, and reporting procedures.
☐ Maintain training records for compliance documentation.
9. Document a System Security Plan (SSP)
An SSP is a foundational document required under NIST 800-171 and CMMC. It outlines your environment, systems, and how CMMC requirements are being met.
📌 Checklist Item:
☐ Create or update your SSP with detailed descriptions of each control and how it's implemented.
☐ Include network diagrams, system boundaries, and technology descriptions.
☐ Store the SSP securely and keep it current.
10. Maintain a Plan of Action and Milestones (POA&M)
If your organization isn't fully compliant yet, a POA&M outlines the steps you're taking to close the gaps. While not allowed for certification delays in CMMC Level 2+ assessments, a POA&M is still a useful internal tracking tool.
📌 Checklist Item:
☐ List incomplete controls with target dates and remediation plans.
☐ Assign ownership for each action item.
☐ Regularly review and update progress.
11. Prepare for the Assessment Process
Depending on your required CMMC level, you'll need to either perform a self-assessment or undergo a third-party evaluation by a C3PAO (Certified Third Party Assessment Organization).
📌 Checklist Item:
☐ Collect and organize all documentation and evidence.
☐ Conduct a mock assessment or internal audit.
☐ Engage a C3PAO early to schedule an official assessment, if applicable.
☐ Be prepared for follow-up questions and requests for clarification.
12. Implement Continuous Monitoring
CMMC is not a one-and-done framework. You must continuously monitor your security posture and adapt as threats evolve.
📌 Checklist Item:
☐ Set up regular reviews of controls, logs, and system configurations.
☐ Schedule periodic risk assessments and internal audits.
☐ Stay informed about changes to CMMC, NIST, and DoD requirements.
• Final Thoughts
Achieving CMMC certification is not simply a checkbox activity-it's an ongoing commitment to cybersecurity excellence. A detailed CMMC compliance checklist can help you reduce risk, improve efficiency, and prepare for the rigorous expectations of the DoD contracting environment.
By taking a proactive and structured approach-backed by accurate documentation, strong policies, and technical enforcement-you can turn compliance into a strategic advantage. Whether you're in early preparation or final review, this checklist will serve as your go-to resource for navigating the CMMC landscape.
Office 7602 182-184 High Street North East Ham London E6 2JA
Finixio Digital is a UK-based remote-first Marketing & SEO Agency helping clients worldwide. In only a few short years, we have grown to become a leading Marketing, SEO, and Content agency.
Contact:
Mail: Media.finixiodigital@gmail.com
Phone: +44 7577 509325
This release was published on openPR.
Permanent link to this press release:
Copy
Please set a link in the press area of your homepage to this press release on openPR. openPR disclaims liability for any content contained in this release.
You can edit or delete your press release What Should Be on Your CMMC Compliance Checklist? here
News-ID: 4133510 • Views: …
More Releases from Finixio Digital

Propacks Gives Small Brands a Viable Path to SB 54 Compliance as Recycled Resin …
The Ontario-based sustainable packaging company is closing the verified PCR sourcing gap that has left indie and emerging brands exposed to active AB 793 penalties - with certified recycled bottles, full documentation, and no enterprise minimums.
Company: Propacks (Propack Solutions) Founded by: Queenie Fong, Ontario, CA Certifications: GRS · SCS Global · ISCC Plus Materials offered: PCR PET · PCR HDPE · PCR PP
ONTARIO, CA - Propacks, a woman-owned sustainable packaging…

How B2B SaaS Brands Can Build Authority Beyond Paid Channels
Paid channels can buy attention. They can put your brand in front of the right audience fast. They can fill the pipeline for a while. But rented attention has a short memory. The moment the budget slows down, the noise fades, the clicks thin out, and the momentum starts to slip.
Authority works differently.
Authority stays. It compounds. It turns a brand from another vendor in the market into a name buyers…
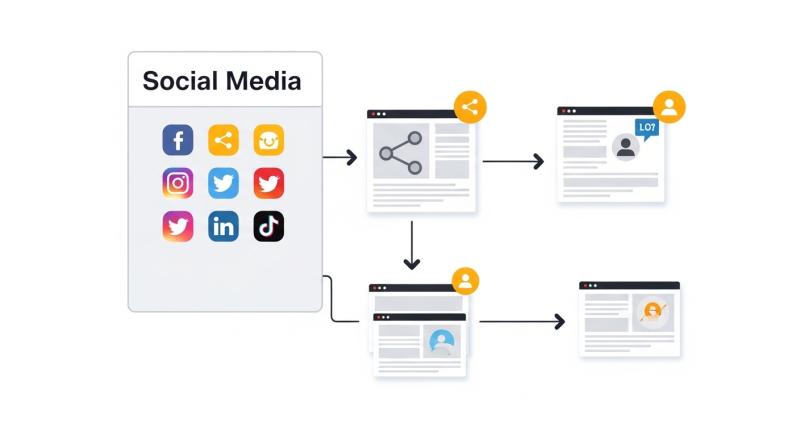
How Does Content Create Traffic Besides Search Rankings?
It seems like traffic follows search rankings. If the page cannot be found on the first page of Google, it is considered underperforming. In reality, that is far from being the case. There are numerous examples of content that continues attracting visitors regardless of the lack of search visibility.
That does not mean that search rankings are irrelevant. Traffic generation and content marketing strategies have changed over the years, and the…

The Art of Personal Expression: Why You Should Customize Your Gifts Online
In a world where convenience often takes priority over sentiment, gift-giving has gradually shifted from thoughtful selection to quick, last-minute purchases. Yet, despite the rise of fast retail and same-day delivery, one powerful trend continues to stand out: the desire to make gifts meaningful. This is where the concept to customize your gifts online (https://corporate-gifts.com.sg) comes into play-blending creativity, personalization, and technology into a single, thoughtful gesture.
Customizing gifts online is…
More Releases for CMMC
Teal Achieves a Perfect 110/110 Score in CMMC Level 2 Assessment
Image: https://www.globalnewslines.com/uploads/2026/04/1776797614.jpg
Teal achieves a perfect 110/110 in its CMMC Level 2 assessment using the same program it delivers to defense contractor clients.
Teal, an independently owned CMMC managed IT services company, has achieved Cybersecurity Maturity Model Certification Level 2 following an independent assessment by an accredited CMMC Third-Party Assessment Organization (C3PAO). The company received a perfect score of 110 out of 110, confirming full implementation of every security control in NIST…
Jaiglo Delivers Perfect 110/110 CMMC Level 2 Score for Defense Contractor Supply …
NY defense contractor passes independent C3PAO assessment with zero deficiencies across all NIST SP 800-171 controls
Valley Cottage, NY - Supplynet Inc., a Defense Industrial Base contractor providing supply chain solutions to the United States defense sector, has achieved Cybersecurity Maturity Model Certification (CMMC) Level 2 following an independent assessment by an accredited CMMC Third-Party Assessment Organization (C3PAO). The company received a perfect score of 110 out of 110, confirming full…
Conviso Inc. Obtains a Perfect CMMC Level 2 Assessment Score!
March 21, 2026 - Luray, Virginia - We are excited to announce Conviso Inc, has achieved a perfect score on our Cybersecurity Maturity Model Certification (CMMC) Level 2 Assessment conducted by a third-party assessment organization. Conviso achieves this certification several months before the requirement for a third-party assessment is required. Receiving this certification reflects our company's unwavering commitment to resilience and excellence in cybersecurity.
Conviso's President, Uday Malhan, stated, "This was…
Teal Launches New CMMC Brand That Empowers Defense Contractors
Image: https://www.globalnewslines.com/uploads/2026/02/1771866538.jpg
Teal, an independently owned managed IT services and managed compliance advisor, launched its new brand, Teal CMMC. Designed specifically for defense contractors and suppliers, Teal CMMC assists small- to medium-sized businesses from the beginning of CMMC Level 2 readiness through to the growth stage - helping contractors strengthen their compliance posture and overall competitiveness.
Building on Teal's 26-year legacy of supporting regulated businesses and experience as a Cyber AB-approved RPO,…
SecurePoint USA Opens Controlled Beta for 2026 CMMC Level 2 and ITAR Visitor Com …
UNITED STATES, January 22, 2026, SecurePoint USA announced that SecurePoint USA is now open for controlled beta access for defense contractors, aerospace manufacturers, and regulated suppliers preparing for 2026 compliance expectations tied to CMMC Level 2, NIST SP 800-171, DFARS, and export control programs including ITAR and EAR.
As requirements tighten, many teams face the same operational gap, written policy exists, but evidence is scattered across spreadsheets, email threads, badge logs,…
VLC Solutions Releases Cybersecurity Maturity Model Certification (CMMC) Solutio …
VLC Solutions, a leading provider of Digital solutions, is excited to announce the release of their new Cybersecurity Maturity Model Certification (CMMC) solutions. Designed to help businesses achieve compliance with the CMMC framework, VLC's solutions provide a comprehensive approach to cybersecurity that is tailored to each client's unique needs.
The CMMC framework was developed by the U.S. Department of Defense (DoD) to ensure that contractors and subcontractors meet a minimum level…
