Press release
Automated Breach and Attack Simulation Market Development Trends, Threats, Opportunities and Competitive Landscape in 2028
The Automated Breach and Attack Simulation Market study analysis offers a complete evaluation of the Automated Breach and Attack Simulation Market which contains facts, thoughtful insights, historical data, and statistically supported and industry-validated market information. Automated Breach and Attack Simulation Market analyses also contain forecasts that are derived from an appropriate set of conventions and practices.This research report is involved with the widespread usage of both primary & secondary data sources. The research report includes the analysis of several factors that are affecting the industry, along with the government policy, competitive landscape, and market environment, present trends in the market, technological development, upcoming technologies, and technical progress in related industries, and market risks, opportunities, market barriers, and challenges.
Click here to get sample of the premium report: https://www.quincemarketinsights.com/request-sample-56237?utm_source=Openpr/SA
With figures and tables, it analyses the Automated Breach and Attack Simulation market. This research delivers key statistics on the state of the market and is a valuable source of guidance and direction for manufacturers and individuals interested in this market.
The report also offers recent market dynamics, such as driving factors, restraining factors, and market news such as mergers, investments, and acquisitions. It offers market size (volume and value), market revenue, growth rate, and integrates both quantitative and qualitative methods to make micro and macro estimations in different regions or countries.
The study can aid in understanding the industry and then make strategies for business growth accordingly. In the strategy analysis, it offers insights from marketing channel and industry positioning to potential growth strategies, offering in-depth analysis for new participants or existing players in the Automated Breach and Attack Simulation market.
Get ToC for the overview of the premium reporthttps://www.quincemarketinsights.com/request-toc-56237?utm_source=Openpr/SA
Automated Breach and Attack Simulation Market Segmentation
The entire Automated Breach and Attack Simulation market has been sub-categorized by different segments and sub-segments. The report offers an analysis of these subsections with respect to the regional segmentation. This research report will keep vendors informed and help them identify the target demographics for a service or product. The Global Automated Breach and Attack Simulation Market can be segmented By Offerings (Solutions, Services), By Application (Patch Management, Configuration Management, Threat Intelligence), By End Users (Enterprises, Service Providers, Data Centers, Others)
The report contains Porter’s Five Forces Model, Value Chain Analysis, and Market Attractiveness Analysis. These tools help get a clear image of the industry’s structure and assess the competitive attractiveness at an international level. Furthermore, these tools also offer an inclusive assessment of the overall application/product segment in the global market of Automated Breach and Attack Simulation.
Regional Analysis of Automated Breach and Attack Simulation Market
This section includes regional segmentation that accentuates the recent and future demand for Automated Breach and Attack Simulation market across North America, Europe, Asia-Pacific, Middle East & Africa, and South America. Further, the study focuses on the demand for each application segment over all the prominent regions.
Competitive Scope
The research report also contains complete profiles of the major players in the market and an in-depth view of the competitive landscape across the globe. The key players in the Automated Breach and Attack Simulation market include AttackIQ, XM Cyber, Qualys, Rapid7, DXC Technology, Skybox Security, SafeBreach, Firemon, NopSec, Threatcare, Mazebolt, and Scythe. This section comprises a holistic view of the competitive landscape that comprises various strategic growths such as future capacities, partnerships, financial overviews, key mergers & acquisitions, collaborations, new product developments, new product launches, and other expansions.
Research Methodology:
This research report has been prepared by collecting data on the basis of primary and secondary research techniques. Secondary research has been done by using several sources that cover (but not limited to) Paid Data Sources, SEC Filings, Technical Journals, Company Websites, Financial Reports, and other industry publications.
Further, the report provides niche insights for a decision about every possible segment, helping in the strategic decision-making process and market size estimation of the Automated Breach and Attack Simulation market on a regional and global basis. Unique research designed for market size estimation and forecast is used for the identification of major companies operating in the market with related developments. The report has an exhaustive scope to cover all the possible segments, helping every stakeholder in the Automated Breach and Attack Simulation market.
Market Segmentation:
By Offerings:
Solutions
Services
By Application:
Patch Management
Configuration Management
Threat Intelligence
By End Users:
Enterprises
Service Providers
Data Centers
Others
By Region:
North America
By Country (US, Canada, Mexico)
By Offerings
By Application
By End Users
Western Europe
By Country (Germany, UK, France, Italy, Spain, Rest of Western Europe)
By Offerings
By Application
By End Users
Eastern Europe
By Country (Russia, Turkey, Rest of Eastern Europe)
By Offerings
By Application
By End Users
Asia Pacific
By Country (China, Japan, India, South Korea, Australia, Rest of Asia Pacific)
By Offerings
By Application
By End Users
Middle East
By Country (UAE, Saudi Arabia, Qatar, Iran, Rest of Middle East)
By Offerings
By Application
By End Users
Rest of the World
By Region (South America, Africa)
By Offerings
By Application
By End Users
Contact:
Quince Market Insights
Office No- A109
Pune, Maharashtra 411028
Phone: APAC +91 706 672 4848 / US +1 208 405 2835 / UK +44 1444 39 0986
Email: sales@quincemarketinsights.com
Web: https://www.quincemarketinsights.com
ABOUT US:
QMI has the most comprehensive collection of market research products and services available on the web. We deliver reports from virtually all major publications and refresh our list regularly to provide you with immediate online access to the world’s most extensive and up-to-date archive of professional insights into global markets, companies, goods, and patterns.
This release was published on openPR.
Permanent link to this press release:
Copy
Please set a link in the press area of your homepage to this press release on openPR. openPR disclaims liability for any content contained in this release.
You can edit or delete your press release Automated Breach and Attack Simulation Market Development Trends, Threats, Opportunities and Competitive Landscape in 2028 here
News-ID: 2334262 • Views: …
More Releases from QUINCE MARKET INSIGHTS

Premium Bicycles Market Demand, Future Trends, Size, Share and Outlook till 2032 …
Premium Bicycles Market Size & Industry Trends Shaping 2032
A more concise understanding of the Premium Bicycles Market dynamics is provided by QMI. A detailed analysis of market statistics covering both present and emerging trends. The report includes Porter's Five Forces to analyze the prominence of various features such as the understanding of both the suppliers and customers, risks posed by various agents, the strength of competition, and promising emerging businesspersons…

Smart Bicycle Market Detail Analysis focusing on Application, Types and Regional …
Smart Bicycle Market Size & Industry Trends Shaping 2032
A more concise understanding of the Smart Bicycle Market dynamics is provided by QMI. A detailed analysis of market statistics covering both present and emerging trends. The report includes Porter's Five Forces to analyze the prominence of various features such as the understanding of both the suppliers and customers, risks posed by various agents, the strength of competition, and promising emerging businesspersons…
Battery Technology Market: Drivers, Revenue, Application Industry Demand Analysi …
Battery Technology Market Size & Industry Trends Shaping 2032
A more concise understanding of the battery technology market dynamics is provided by QMI. A detailed analysis of market statistics covering both present and emerging trends. The report includes Porter's Five Forces to analyze the prominence of various features such as the understanding of both the suppliers and customers, risks posed by various agents, the strength of competition, and promising emerging businesspersons…
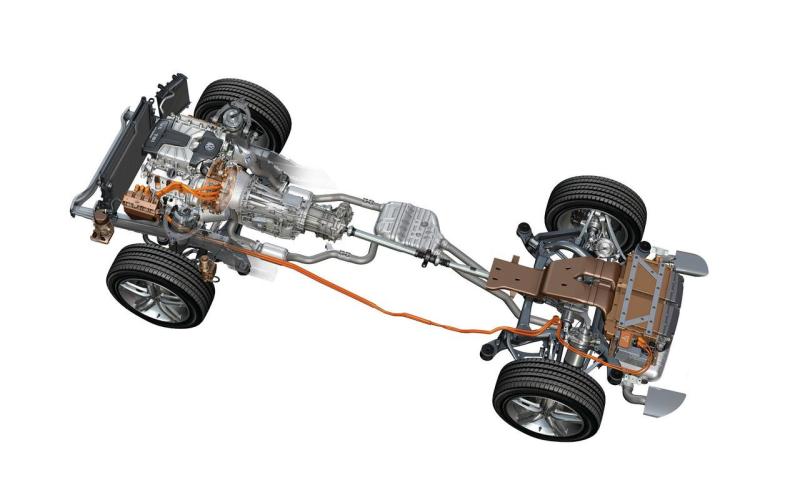
Global Automotive Powertrain Market Size, Share, Industry Forecast 2032 | Toyota …
The most recent report published by QMI indicates that the "Automotive Powertrain Market" is likely to accelerate significantly in the next few years. The Automotive Powertrain Market report gives a purposeful depiction of the area by the practice for research, amalgamation, market size, overview, and review of data taken from various sources. The Automotive Powertrain Market study includes information on market factors such as the market dynamics, drivers, restraints, challenges,…
More Releases for Breach
Key Trends Reshaping the Automated Breach And Attack Simulation Market: Rapid Te …
Use code ONLINE20 to get 20% off on global market reports and stay ahead of tariff changes, macro trends, and global economic shifts.
Automated Breach And Attack Simulation Market Size Growth Forecast: What to Expect by 2025?
The market size of automated breach and attack simulation has seen a significant surge in the past few years. It is projected to rise from $0.69 billion in 2024 to $0.92 billion in 2025, increasing…
Key Trends Reshaping the Automated Breach And Attack Simulation Market: Rapid Te …
Stay ahead with our updated market reports featuring the latest on tariffs, trade flows, and supply chain transformations.
Automated Breach And Attack Simulation Market Size Growth Forecast: What to Expect by 2025?
There has been a rapid surge in the size of the automated breach and attack simulation market in the past few years. It is projected to grow from $0.69 billion in 2024 to $0.93 billion in 2025, with a compound…
What Constitutes a Breach of Contract Under Colorado Law?
Contracts are the backbone of business, employment, real estate, and many other transactions in Colorado. When one party fails to live up to their side of the agreement, the other party may suffer financial harm or disruption, and may have legal grounds to file a claim for breach of contract. But what exactly qualifies as a breach under Colorado law?
Understanding what constitutes a breach of contract is essential, whether you're…
Complex Security Threats Drive Growth In Automated Breach And Attack Simulation …
The Automated Breach And Attack Simulation Market Report by The Business Research Company delivers a detailed market assessment, covering size projections from 2025 to 2034. This report explores crucial market trends, major drivers and market segmentation by [key segment categories].
What Is the Current Automated Breach And Attack Simulation Market Size and Its Estimated Growth Rate?
In recent times, there has been considerable growth in the size of the automated breach and…
Breach and Attack Simulation Solutions Market Key Innovations for 2032
The Breach and Attack Simulation (BAS) Solutions market is rapidly evolving, becoming an essential component of cybersecurity strategies for organizations worldwide. With the increasing frequency and sophistication of cyber threats, the relevance of these solutions has never been more pronounced. BAS solutions allow enterprises to simulate attacks, assess vulnerabilities, and strengthen their security posture proactively. This proactive approach is pivotal in a landscape where cybercriminals continuously develop new tactics to…
Global Breach And Attack Simulation Tools Market Size by Application, Type, and …
USA, New Jersey- According to Market Research Intellect, the global Breach And Attack Simulation Tools market in the Internet, Communication and Technology category is projected to witness significant growth from 2025 to 2032. Market dynamics, technological advancements, and evolving consumer demand are expected to drive expansion during this period.
The Breach and Attack Simulation (BAS) Tools Market is experiencing significant growth due to the increasing frequency and sophistication of cyber threats.…
