Press release
Cybersecurity Management Consulting Services Market Size 2019 Outlook 2025 Allianz , AXA , Ping An , Assicurazioni Generali , China Life Insurance , Metlife
Global Cybersecurity Management Consulting Services Market 2019 gives exceptional insight into the for the forecast from (2019-2025). The analysis has covered the factors which are contributing to the growth of the worldwide Cybersecurity Management Consulting Services market. Highlighting the fundamental tendencies such as drivers, Cybersecurity Management Consulting Services market trends, along with restraints which are currently influencing. An indicator has been provided by this report to the pursuers around the latest update on the industry.Objectives of this research report:
Identifying the market needs
Identifying the customers as well as potential customers
Gives more focus on market growth opportunities
Estimation of cost structure and market size
Identifying demanding region with analysis of specific countries
Get free sample report @ http://www.supplydemandmarketresearch.com/home/contact/35436?ref=Sample-and-Brochure&toccode=SDMRSE35436&utm_source=sis
The key players covered in this study
• AT&T
• TCS
• Hewlett Packard Enterprise
• PwC
• Vumetric
• Wipro
• IT Governance
• RSA
• Telos
• MARSH LLC. ALL RIGHTS RESERVED
• AT&T Intellectual Property
• SecureWorks, Inc.
• Deloitte
The study objectives of this report are:
To analyze global Cybersecurity Management Consulting Services status, future forecast, growth opportunity, key market and key players.
To present the Cybersecurity Management Consulting Services development in United States, Europe and China.
To strategically profile the key players and comprehensively analyze their development plan and strategies.
To define, describe and forecast the market by product type, market and key regions.
Market segment by Type, the product can be split into
• Type I
• Type II
Market segment by Application, split into
• Client's Market Capitalization: Less Than 300 Million
• Client's Market Capitalization: 300-2000 Million
• Client's Market Capitalization: 2000-5000 Million
• Client's Market Capitalization: Greater Than 5000 Million
• Government
Enquire before purchase@: https://www.supplydemandmarketresearch.com/home/purchase?code=SDMRSE35436
Table of contents:
1 Report Overview
1.1 Study Scope
1.2 Key Market Segments
1.3 Players Covered
1.4 Market Analysis by Type
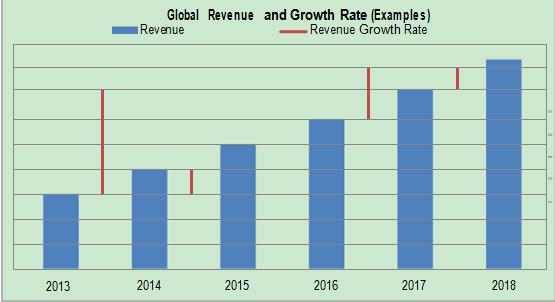
1.4.1 Global Cybersecurity Management Consulting Services Market Size Growth Rate by Type (2013-2025)
1.4.2 Type I
1.4.3 Type II
1.5 Market by Application
1.5.1 Global Cybersecurity Management Consulting Services Market Share by Application (2013-2025)
1.5.2 Client's Market Capitalization:
About us
We have a strong network of high powered and experienced global consultants who have about 10+ years of experience in the specific industry to deliver quality research and analysis.
Having such an experienced network, our services not only cater to the client who wants the basic reference of market numbers and related high growth areas in the demand side, but also we provide detailed and granular information using which the client can definitely plan the strategies with respect to both supply and demand side.
Canada Office:
302-20 Misssisauga Valley Blvd, Missisauga, L5A 3S1, Toronto
Contact Us
Email- info@supplydemandmarketresearch.com
Website-http://www.supplydemandmarketresearch.com/
Phone Number: +1-276-477-5910
This release was published on openPR.
Permanent link to this press release:
Copy
Please set a link in the press area of your homepage to this press release on openPR. openPR disclaims liability for any content contained in this release.
You can edit or delete your press release Cybersecurity Management Consulting Services Market Size 2019 Outlook 2025 Allianz , AXA , Ping An , Assicurazioni Generali , China Life Insurance , Metlife here
News-ID: 1735666 • Views: …
More Releases from Supply Demand Market Research

Germany Waste Heat Recovery Systems is anticipated to reach USD 2150 Million by …
The Germany Waste Heat Recovery Systems (WHRS) is anticipated to reach USD 2150 million by 2030 growing at a CAGR of 5.7% from 2024-2030. Continued expansion post-2026 aligns with Germany's decarbonization trajectory, as operators increasingly prioritize heat-recovery to reduce fuel consumption and comply with tightening carbon-intensity expectations.
By technology, the exchange waste heat recovery boilers market size is anticipated to reach USD 710 million by 2030. Exchange/WH Boilers and SRC (Steam…

South Korea Flounder Market Anticipated to grow at a CAGR of 8% from 2023-2030
The South Korea flounder is anticipated to grow at a CAGR% of 8.0% from 2022-2030. The factors contributing towards the high growth are flounders such as halibut and turbot high-protein and low-calorie food, helps to re-solve the nutritional imbalance from diet because of its rich minerals, carbohydrates and vitamins despite low-calorie. They also offer medical benefits as liver of halibut contains lots of vitamin B1 and B2, which is effective…

Global Flounder Market Anticipated to reach USD 56 Billion by 2030
The global flounder market is anticipated to reach USD 56 Billion by 2030, growing at a CAGR% of 8.0% from 2022-2030. The factors contributing towards the high growth are flounders such as halibut and turbot high-protein and low-calorie food, helps to re-solve the nutritional imbalance from diet because of its rich minerals, carbohydrates and vitamins despite low-calorie. They also offer medical benefits as liver of halibut contains lots of vitamin…

Global Seafood Market Anticipated to reach USD 730 Billion by 2030
The global seafood market is anticipated to reach USD 730 Billion by 2030, growing at a CAGR% of 8.9% from 2022-2030. The factors contributing towards the high growth are increased disposable income, awareness of fish being used as an ingredient in healthy food is growing. USA the government plans to sanction illegal fishing activities, actively promote fair trade, and promote strategies to promote the fishing industry through detailed strategies such…
More Releases for Cybersecurity
Fortem Cybersecurity, the New Global Cybersecurity Brand from Maguen Group, Offi …
Fortem Cybersecurity brings a new era of digital defense.
Image: https://www.globalnewslines.com/uploads/2025/11/c0679b6403ecd7de771af2a356c54f29.jpg
Maguen Group [https://www.maguengroup.com/?lang=en], a leading Mexican private security company with over 17 years of operational excellence and ethical leadership, is proud to announce the launch of its new global cybersecurity brand, Fortem Cybersecurity [https://fortem-security.com/]. This launch comes as part of Maguen Group's plans to expand its presence and democratize cybersecurity.
With the launch of Fortem Cybersecurity, Maguen Group continues its commitment to…
Rising Global Cybersecurity Threats Propel Growth In Military Cybersecurity Mark …
The Military Cybersecurity Market Report by The Business Research Company delivers a detailed market assessment, covering size projections from 2025 to 2034. This report explores crucial market trends, major drivers and market segmentation by [key segment categories].
What Is the Military Cybersecurity Market Size and Projected Growth Rate?
The size of the military cybersecurity market has seen significant growth recently. The market is predicted to increase from a worth of $14.05 billion…
Rising Global Cybersecurity Threats Propel Growth In Military Cybersecurity Mark …
What market dynamics are playing a key role in accelerating the growth of the military cybersecurity market?
The surge in cyberattacks is projected to drive the expansion of the military cybersecurity market. A cyberattack, an illicit attempt to infiltrate a computer system or network to cause disruption, can result in data theft, deliberate machine impairment, or use a breached system to launch further attacks. The military's smooth operation hinges on the…
Top Cybersecurity Expert Nandy Bo Publishes Groundbreaking Freelancing Guide for …
NYC, New York, USA - Renowned cybersecurity consultant and top-rated Upwork freelancer, Nandy Bo, has launched his highly anticipated book, Master Upwork: Achieve Financial Freedom Through a Freelance Cybersecurity Career . This comprehensive guide provides aspiring and seasoned freelancers with the tools and strategies needed to thrive in today's competitive freelance economy, particularly in high-demand fields like cybersecurity and compliance.
With over 16 years of experience, Nandy Bo has established himself…
Cybersecurity Mesh Market Report 2024 - Cybersecurity Mesh Market Demand, Trends …
"The Business Research Company recently released a comprehensive report on the Global Cybersecurity Mesh Market Size and Trends Analysis with Forecast 2024-2033. This latest market research report offers a wealth of valuable insights and data, including global market size, regional shares, and competitor market share. Additionally, it covers current trends, future opportunities, and essential data for success in the industry.
According to The Business Research Company's, The cybersecurity mesh market size…
Cybersecurity Experts Provide Insight on the ROI of Managed Cybersecurity Servic …
Image: https://www.getnews.info/wp-content/uploads/2024/09/1727067882.jpeg
Cybersecurity professionals detail how managed cybersecurity services can provide significant returns on investment (ROI) by offering cost-effective, risk-reducing solutions that enhance an organization's security posture.
Columbia, MD - September 23, 2024 - Shield 7, a leader in cybersecurity services [https://shield7.com/], has recently released a blog titled "The ROI of Managed Cybersecurity Services: A Comparative Analysis." This comprehensive analysis explores how managed cybersecurity services can offer significant returns on investment (ROI)…